Zero Trust Protocols (ZTPs): How They Work and Why They Matter
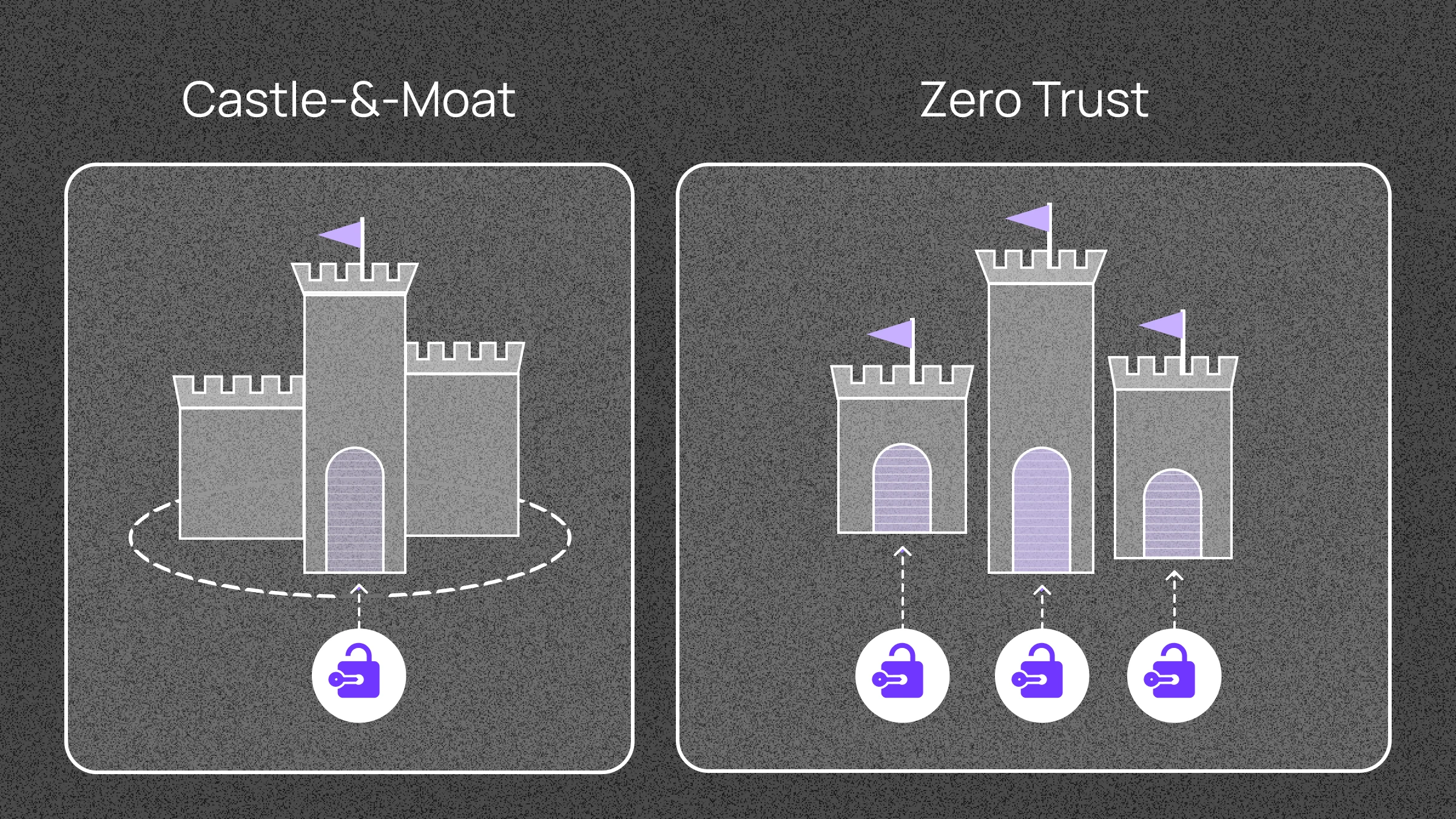
Zero Trust vs. Castle-and-Moat
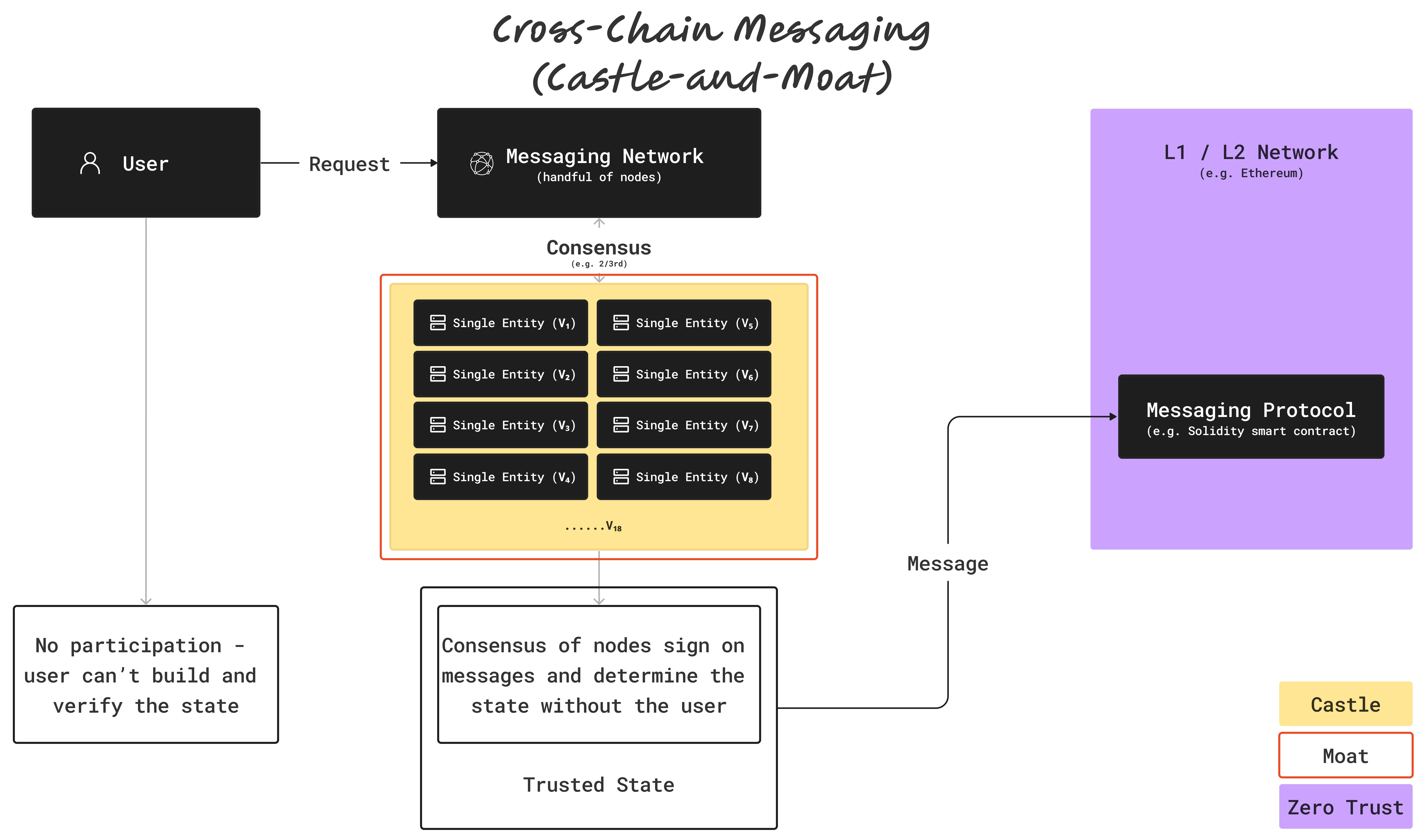
Zero Trust architecture represents a modern network security approach emphasizing verification of all interactions without inherent trust assumptions. In contrast, the Castle-and-Moat model establishes a secure perimeter around trusted internal networks, granting extensive access once inside. While effective in simpler environments, this older approach struggles to handle today's complex and interconnected digital landscape.
Zero Trust was developed to address Castle-and-Moat vulnerabilities. Every entity, whether inside or outside the network, is considered untrustworthy until proven otherwise.
Zero Trust in Web3: A Natural Fit
Since Bitcoin's inception, blockchain technology has used a Zero Trust approach. Users can independently verify every transaction back to the beginning, eliminating reliance on trusted authorities.
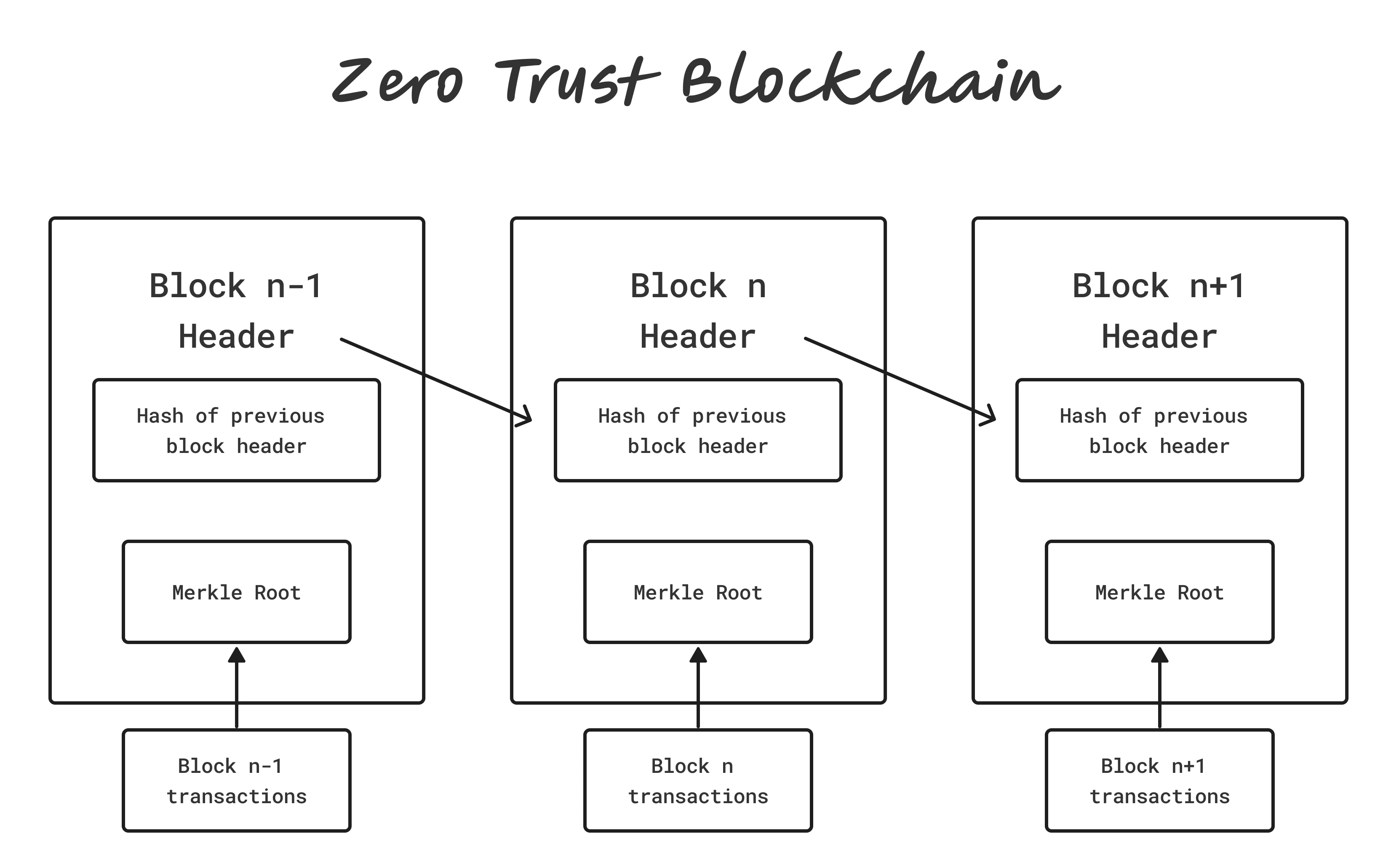
The contrast becomes clear when comparing a hypothetical "Castleum" blockchain (Castle-and-Moat model) with Ethereum's Zero Trust architecture, where users sign transactions, and validators only include them in blocks after verifying their authenticity.
The Sovereignty and Honeypot Problems
As blockchain networks proliferate, cross-chain interoperability creates challenges. The "Sovereignty Problem" arises from the need to connect independent blockchain networks, necessitating trust in a third party.
Additionally, these solutions create lucrative targets for attackers, known as the "Honeypot Problem."
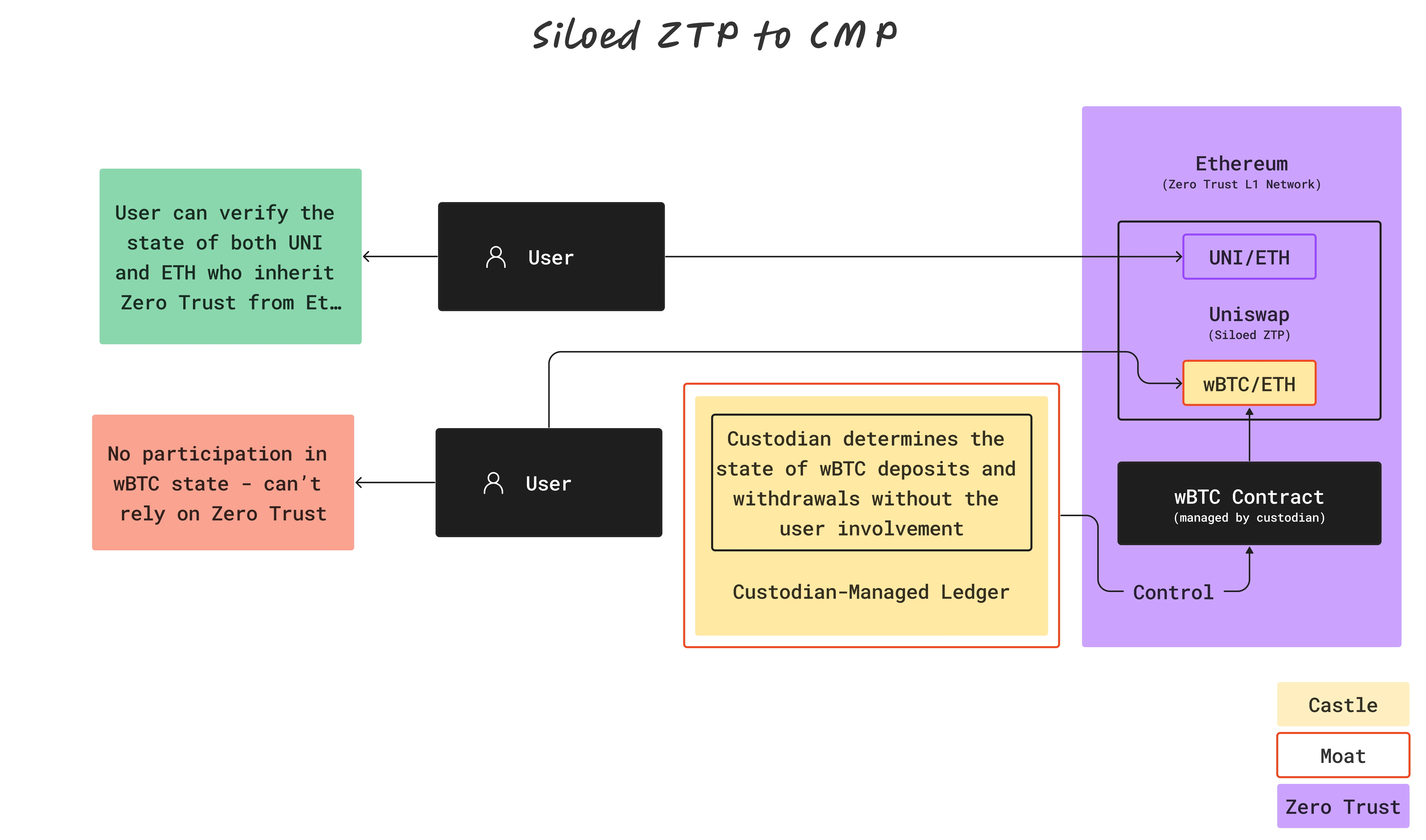
Siloed ZTPs
ZTPs are Web3 protocols that operate using a Zero Trust architecture. Within single blockchains, they maintain Zero Trust for native assets only.
Uniswap exemplifies a Siloed ZTP when swapping native Ethereum assets like UNI and ETH. However, swapping ETH for wrapped Bitcoin (wBTC) changes the situation since wBTC relies on centralized custody, making it function as a Castle-and-Moat Protocol.
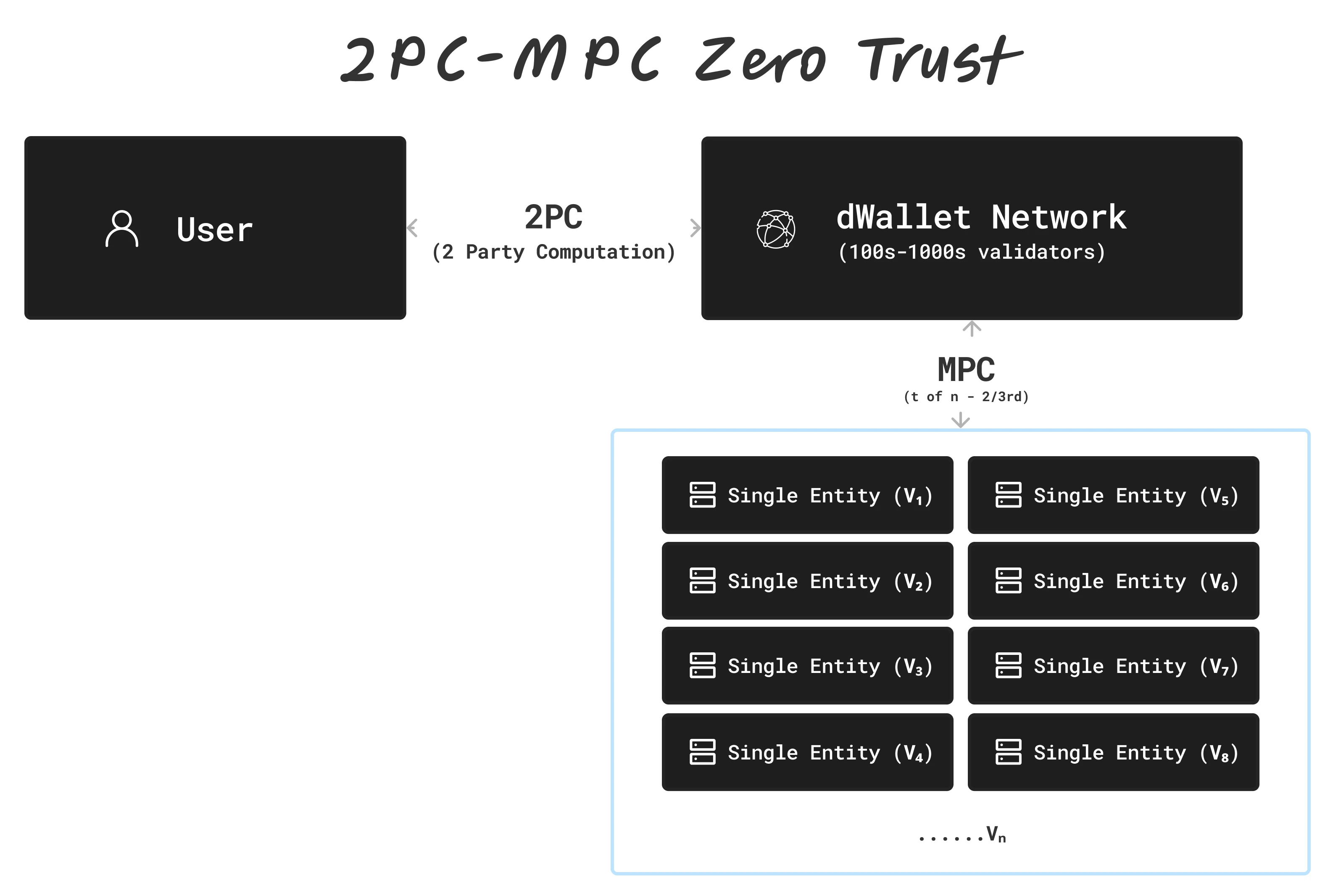
2PC-MPC: The Future of ZTPs
Ika uses advanced cryptography to maintain Zero Trust across networks. 2PC-MPC is a cryptographic scheme that allows two parties (in this case, the user and the Ika Network) to jointly generate a signature to any network.
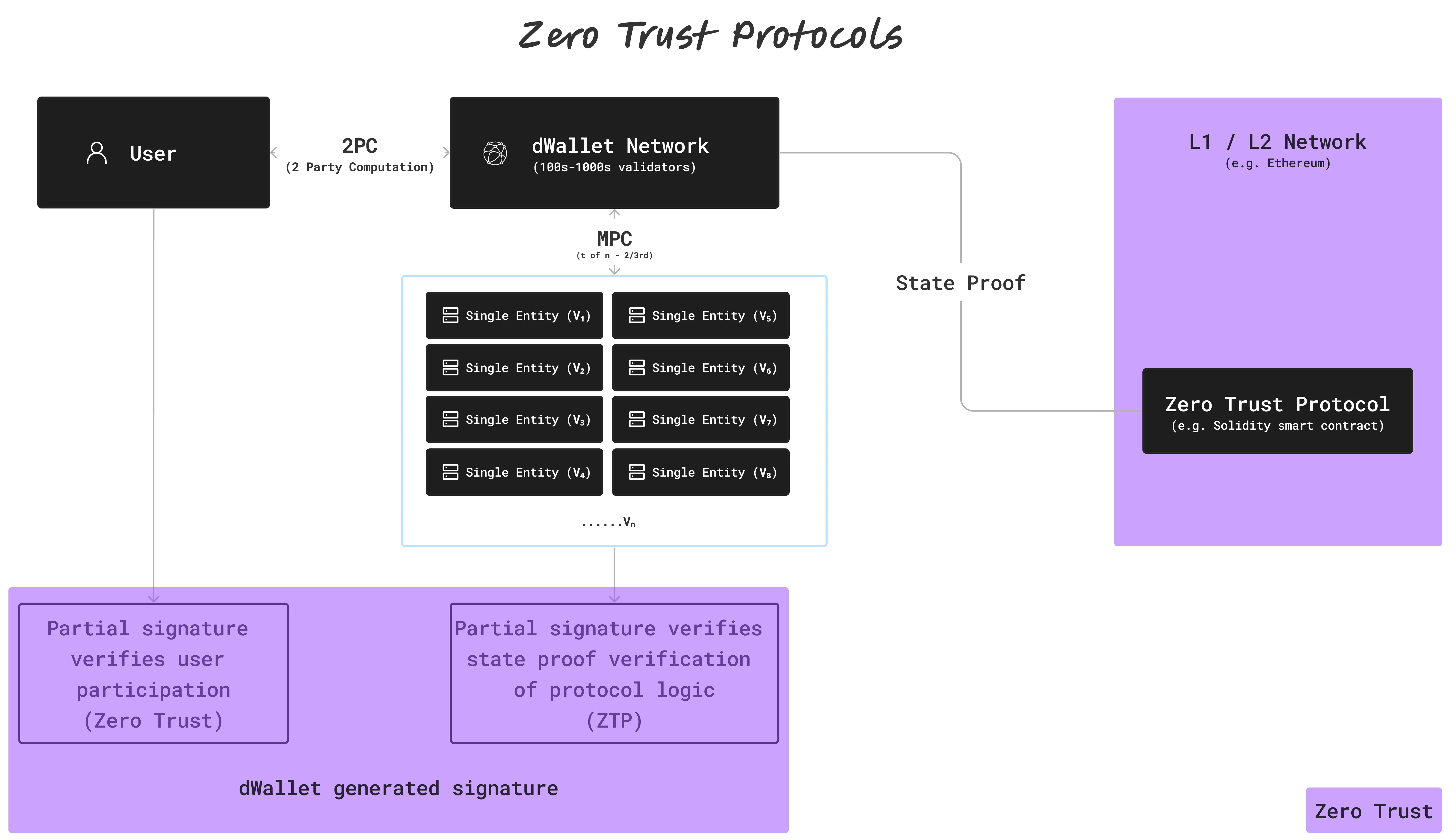
How ZTPs Work
- User and Network Participation: Both the user and the Ika Network must participate for transaction validation.
- Decentralized Verification: The network comprises numerous nodes verifying actions.
- Cross-Chain Interactions: ZTPs enable secure interactions across different blockchains.
Real-World Applications of ZTPs
Vitalik Buterin has expressed concerns about cross-chain security, noting "fundamental limits to the security of bridges that hop across multiple 'zones of sovereignty'."
ZTPs enable multi-chain functionality without Castle-and-Moat architecture. With dWallets, builders on L1s and L2s can program native BTC as part of their ZTPs. No bridging, no wrapping.
Conclusion
Zero Trust Protocols (ZTPs) are essential for maintaining security and integrity in a multi-chain Web3. Ika's 2PC-MPC cryptographic protocol provides infrastructure for implementing ZTPs across blockchains, supporting the development of secure decentralized applications.